01Why Native Salesforce Architecture Is a Security Requirement, Not a Feature
When evaluating WhatsApp and SMS apps on Salesforce AppExchange, the single most important question is: where does my data go? Most buyers focus on features — bulk messaging, AI, templates. Security teams focus on data flow. And the answer to 'where does my data go?' separates native apps from middleware-based apps in ways that have serious enterprise compliance implications.
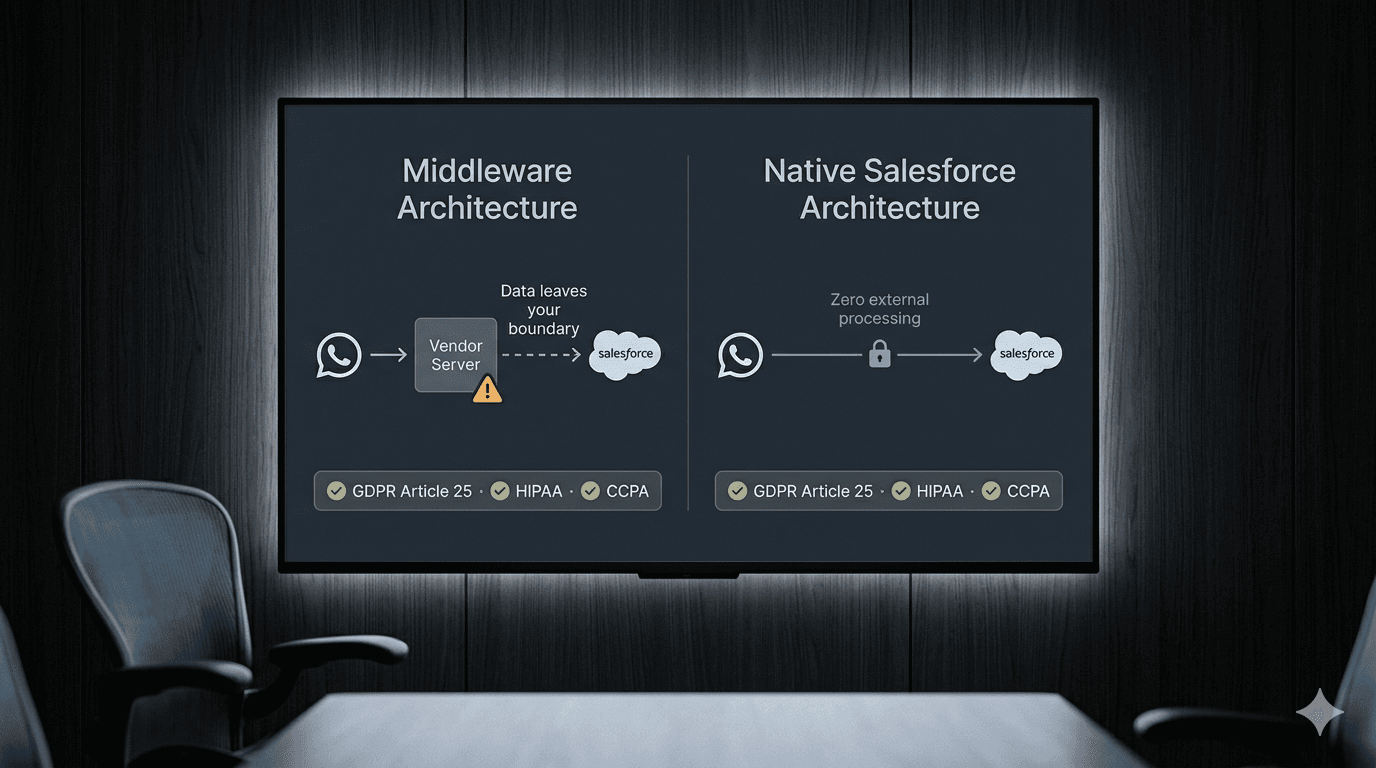
A native Salesforce application is one built entirely on the Salesforce platform using Apex, Lightning Web Components, and Salesforce-native storage. It runs inside your org's trust boundary. Salesforce provides the compute, the storage, and the security layer. The vendor's code runs inside your org — not on external servers.
A middleware-based application routes your data through external servers — typically an AWS or Azure instance controlled by the vendor — before it reaches Salesforce. Your customer conversations pass through a third party that is not covered by your Salesforce Master Subscription Agreement (MSA) or your customers' consent to data processing.
For GDPR, CCPA, HIPAA, and similar frameworks, this distinction is critical. If your data controller obligations require that customer data stays within a specific jurisdiction, a middleware-based app may violate that requirement by routing data through servers in a different country.
0210 Security Questions to Ask Every AppExchange Messaging Vendor
1. Is your application 100% native to Salesforce, or does it use external middleware servers? If external servers: where are they hosted, under what SLA, and are they included in your data processing agreement?
2. Where are customer message logs stored? Are they in Salesforce objects (like CV_Message__c) within my org, or on your servers?
3. Where are API keys (Twilio credentials, Meta access tokens) stored? Are they in Salesforce Named Credentials, or do you hold them on your platform?
4. Has your application passed Salesforce's AppExchange Security Review? Can you share the review certificate or date?
5. What is your data retention policy? Do you retain copies of messages for any period? For what purpose?
6. Does your application use Salesforce's USER_MODE or SYSTEM_MODE for database operations? (USER_MODE enforces object and field-level security; SYSTEM_MODE bypasses it.)
7. What happens to my data if I uninstall your app? Is all data deleted, or retained on your servers?
8. Have you undergone an independent SOC 2 Type II audit? If so, can you share the report summary?
9. How do you handle security vulnerabilities? What is your disclosure process and average patch timeline?
10. Do you support customer-managed encryption keys (CMEK) for stored data within Salesforce?
03Native vs Third-Party Architecture: GDPR Risk Comparison
Under GDPR, a data processor is any party that processes personal data on behalf of the controller. If your WhatsApp messaging app routes customer conversations through its own servers, that vendor is a data processor. You must have a Data Processing Agreement (DPA) with them, list them in your Data Inventory, and ensure they meet adequacy standards for cross-border transfer (especially relevant for EU companies).
With a native Salesforce app like ConnectVogue, the only data processor for message data is Salesforce itself — already covered by your Master Subscription Agreement and Salesforce's Data Processing Addendum (which meets GDPR Article 28 requirements). There is no additional processor to audit or contract with.
For UK-based companies post-Brexit, this distinction matters under UK GDPR. For US companies in California, CCPA defines a 'service provider' relationship that requires a written contract prohibiting the provider from retaining data for their own purposes — native apps satisfy this automatically by design, since they have no access to your data.
04ConnectVogue Security Architecture: Zero-Data Retention Explained
ConnectVogue is a 2nd-Generation Managed Package (2GP), published on Salesforce AppExchange after passing Salesforce's security review. It is built entirely on Apex and Lightning Web Components with no external dependencies for data storage.
API keys are stored in Salesforce External Credentials and Named Credentials — encrypted at rest using Salesforce's standard AES-256 encryption, accessible only by the Salesforce platform's credential manager. No ConnectVogue employee or system can access your Twilio SID, Meta Access Token, or AI provider keys.
Message data is stored exclusively in CV_Message__c and CV_Conversation__c custom objects within your Salesforce org. ConnectVogue's code accesses this data via Apex using USER_MODE for all user-triggered operations (enforcing your existing field-level security and record sharing rules) and SYSTEM_MODE only for webhook processing (inbound message creation), where system-level access is required to create records without a user session.
Inbound webhook calls from Meta and Twilio are validated using HMAC-SHA256 signature verification before any Apex processing — preventing spoofed webhook calls from creating fraudulent message records.
ConnectVogue's zero-data retention policy is not a policy document — it is an architectural fact. There are no ConnectVogue servers that receive your data. There is nothing to retain.
“When evaluating AppExchange messaging apps: ask where your data goes, where your keys are stored, and whether the vendor has passed Salesforce's security review. Native architecture isn't a premium feature — it's the baseline for enterprise compliance. Control your keys, control your data.”
Frequently Asked Questions
What security questions should I ask a Salesforce AppExchange messaging vendor before buying?
What is the difference between a native Salesforce app and a middleware connector for GDPR compliance?
Does a 100% native Salesforce WhatsApp app require a GDPR Data Processing Agreement?
How does ConnectVogue's zero-data retention architecture pass HIPAA and GDPR Article 25 requirements?
Keep Reading
All InsightsWhat Happens to Your WhatsApp Data When You Use 360SMS? A GDPR and Data Residency Audit
Every inbound WhatsApp message routed through a middleware vendor makes that vendor a GDPR data processor. Here is exactly what that means for Salesforce teams in the EU, UK, and UAE — and how native architecture eliminates the risk entirely.
360SMS Alternative in 2026: Why Salesforce Teams Are Switching to BYOK Architecture
360SMS dominates the Salesforce AppExchange with 60,000+ users. But for scaling teams, BYOK architecture cuts messaging costs by 40–60%, keeps all data inside your org, and delivers multi-provider Agentic AI that 360SMS cannot match.